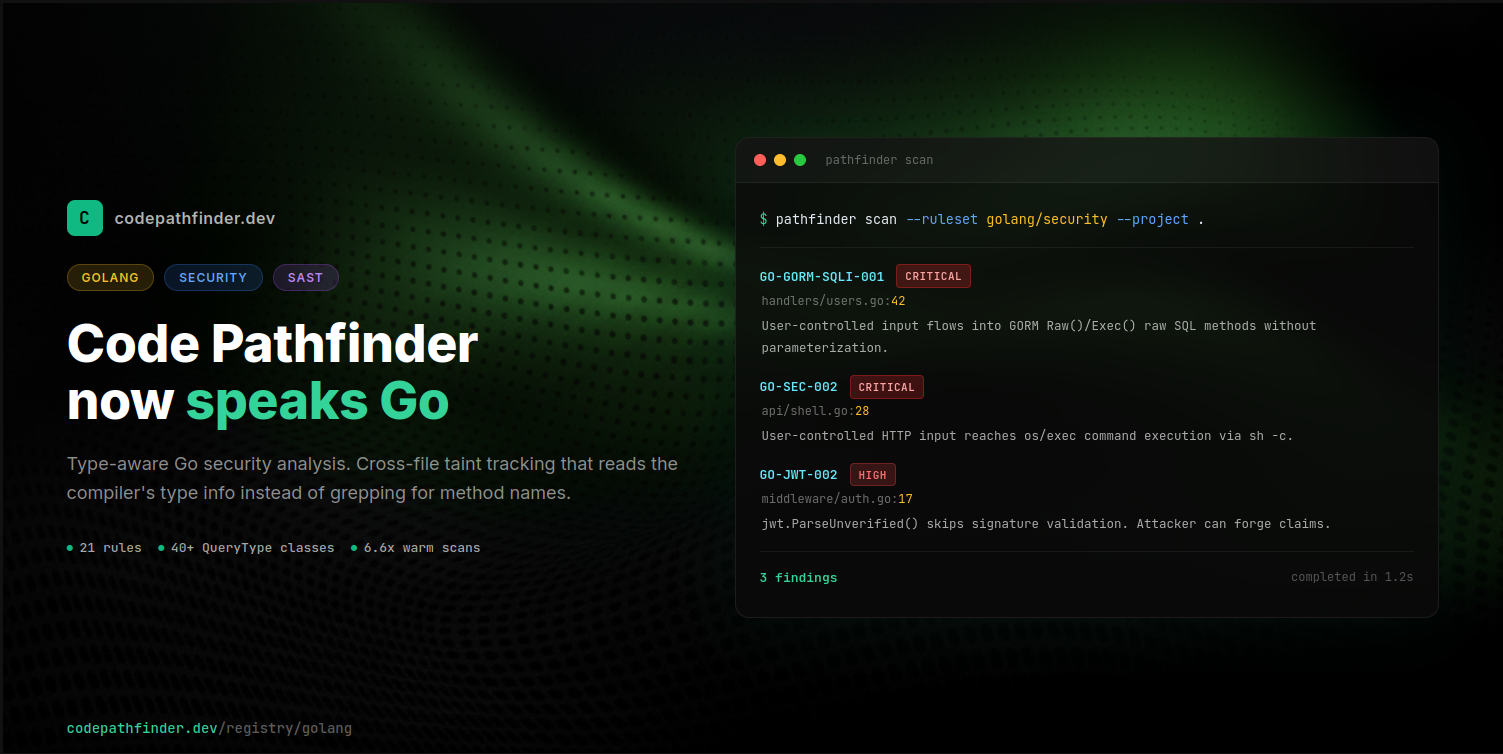
ProductGolangGo SecurityTaint AnalysisOpen Source SAST
Code Pathfinder now speaks Go
Code Pathfinder v2.1.0 adds Go support: 21 security rules, cross-file taint analysis, and type-aware detection across Gin, Echo, Fiber, GORM, sqlx, gRPC, and the standard library.
